
Disaster Recovery
Unleash the power of a cloud first backup & DR solution that guarantees recovery from ransomware with isolated, off-site protection.
Includes InstantData™ technology – providing immediate access to critical data, whether stored on-premise, in the cloud or anywhere.
Stream recovery data back in real time, unthrottled. Vendor agnostic destination giving you total flexibility.
No Capex for equipment or licenses, seamlessly scalable, implemented in minutes. Protect more, for less cost & no effort.
Instant recovery
InstantData™ removes the challenge of moving large volumes of data over the internet by seamlessly streaming data as it’s restored
This gives the immediate availability with requested files re-hydrated on demand and other data restored in the background.
InstantData™ streaming technology allows you to recover massive systems in moments, using a bespoke kernel driver which intercepts read requests from the operating system.
Cloud Archive
Extend the life of hardware without disk upgrades, additional storage arrays or delay. Even prevent the need for more Capex to cope with exponential data growth, seen in every industry sector today.
Dramatically cut primary (expensive) storage costs by offloading data to the cloud, yet still have immediate access to all archived data. Best of all, no user training, added cost or ongoing management is required.
Built into the core, activated via a check box, you’ll wish you found this a time ago! An Instant load off your servers, storage arrays and IaaS.
GDPR - Search & Insight
As your datasets grow and become increasingly decentralised it can be an impossible task to keep track of what is where, why, and how it got there.
Data protection, sovereignty and security are more important than ever. Regulations place considerable strain on already stretched IT resources. Remove the burden by using a compliant service. Simple !
Discover, search and action the entirety of your organisation with data-driven intelligence. We enable you to identify and mitigate data risks wherever they are.
All of these features & more for a simple, per GB monthly fee !
It really can be simple to protect all that you find complex. Even items considered out of reach or scope of existing solutions, can now be protected securely, off-site & searchable.
Utilising Fully compliant system takes away the need for self replication to any required standard. Having 25 years of development, dedicated teams for the complete stack and us on your team. You can’t replicate this for less.

Device Protection
With 30 years of industry leading innovation behind our primary partners, coupled with 20 years experience in the IT sector from our side, we can offer your organisation unparalleled & multi-layered protection. Our aim is to kill FUD. All billed monthly – no Capex required.
You do what you need to do; let us help take care of this for you. Protect without compromise. Ultra lightweight footprint, no impact on productivity or device performance.
Dynamic Threat Defence
Full Disk Encryption (FDE) – GDPR safe
Mobile Device Management (MDM) – Remote wipe and control
Virtualization Security for VMware
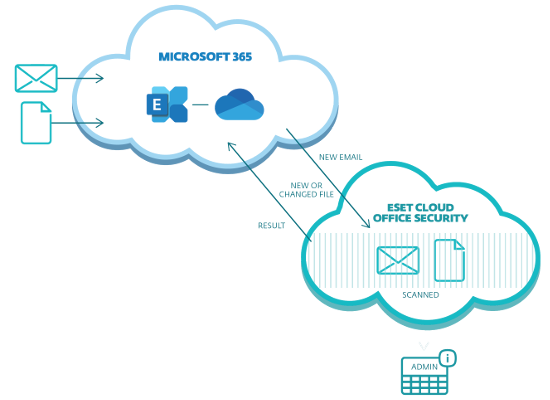
Cloud & Service Protection
Advanced preventative protection for your Office 365 users, email & storage. Anti-phishing, spam filtering & anti-malware for Exchange Online and OneDrive.
Alternate versions for Exchange on-premise & Hybrids, IBM Domino (Notes), Linux BSD Solaris & Kerio.
File Services and other server based applications are protected by Endpoint Security natively. Both the servers and devices accessing them have multiple protection layers available.
ECOS is included with all our PROTECT Complete bundles or as standalone, billed monthly solution.
Intelligent Protection
By acting upon and reacting to sessions & processes throughout their lifecycle, you can prevent and isolate threats from other vulnerable systems. Our carefully selected partners maintain the highest levels of detection & protection in the business – consistently. See VB100
With Advanced Machine Learning, UEFI scanner, Network Attack Protection, Device control, DNA Signature analysis and Sandboxing, before anything has even been executed, you can see why it leads.
Isolation of the infected we all know stops transmission. By using smart, policy driven automation, which reacts to an event or state change which then isolates the infected plus simultaneously updating all other devices enabling identification, we can protect all from emerging and unknown threats before any global update is released.
Managed Protection
If you’re not sure where to start or do know and then hesitate at the thought. That or you simply haven’t the free resources to deliver what you know you need? Well you’re in the right place.
Don’t drown in the drama, we do this for you.
Our techs are highly trained, certified and more importantly experienced. We’ve direct ties to every vendor of every Product & Service we provide.
World leading malware protection with GDPR compliant encryption from as little as 15p per day. Web based administration & reporting console.




